Get your armour on… what you need to know to stay safe!
Like Darwin’s finches, phishing has evolved from a single technique into many highly specialised tactics, each adapted to specific types of targets and technologies. First described in 1987, phishing is now carried out via text, phone, advertising, and-of course-email.
Boiled down, all these tactics exist for the same purpose; to swipe confidential information from an unsuspecting target in order to extract something of value. But knowing about the hugely diverse set of today’s phishing tactics can help ordinary people, home and business internet users alike, to be more prepared for the inevitable instance when they become the target.
Did you know… Almost half of businesses (46%) and a quarter of charities (26%) report having cyber security breaches or attacks in the last 12 months. Like previous years, this is higher among medium businesses (68%), large businesses (75%) and high-income charities (57%)
Cyber Security Breaches report 2020
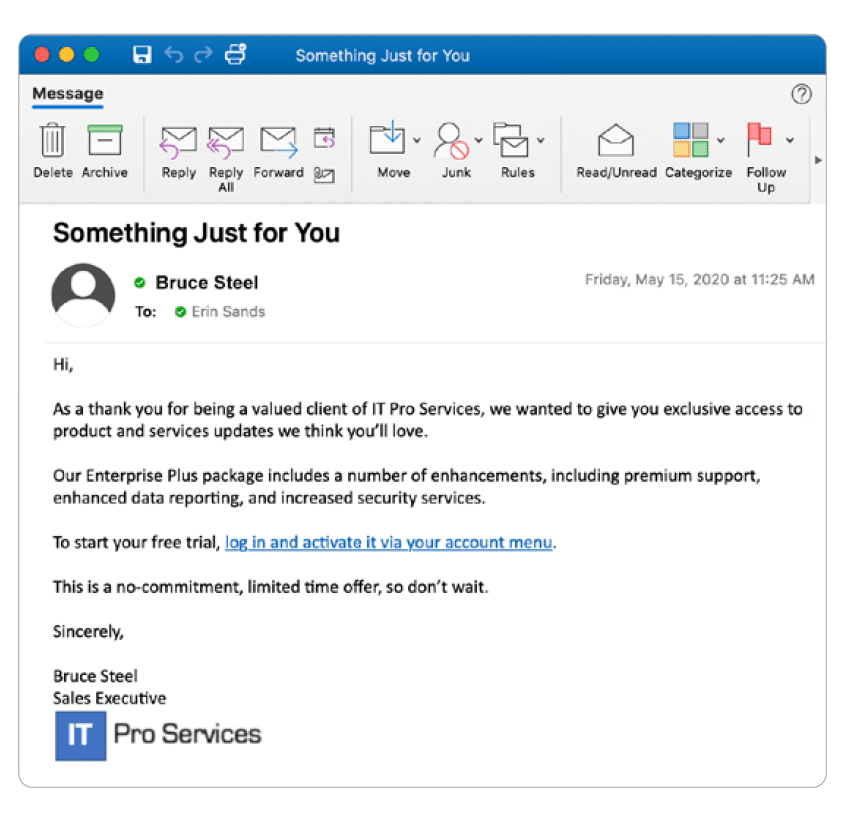
This tactic has, in the past, been more about quantity versus quality. The audience was broad and emails were riddled with noticeable errors. phishing has developed, it’s become more sophisticated and harder to spot. Check out this ‘how to spot a phishing email’
Using the same techniques, this type of phishing introduces nasty bugs by convincing a user to click a link or download an attachment so malware can be installed on a machine. It is currently the most widely used form of phishing attack.
One hallmark of malware phishing is the attachment of a blank document requiring you to enable macros to view its contents, as in the common “package delivery failure”. This is a major red flag.
Where most phishing attacks cast a wide net, hoping to entice as many users as possible to take the bait, spear phishing involves heavy research of a predefined, high-value target—like a CEO, founder, or public persona—often relying on publicly available information for a more convincing ruse.
When the target is sizeable enough, spear phishing is sometimes called ‘whaling’. Below is an example:
SMS-enabled phishing uses text messaging as a method for delivering malicious links, often in the form of short codes, to ensnare smartphone users in their scams. They often look like this…
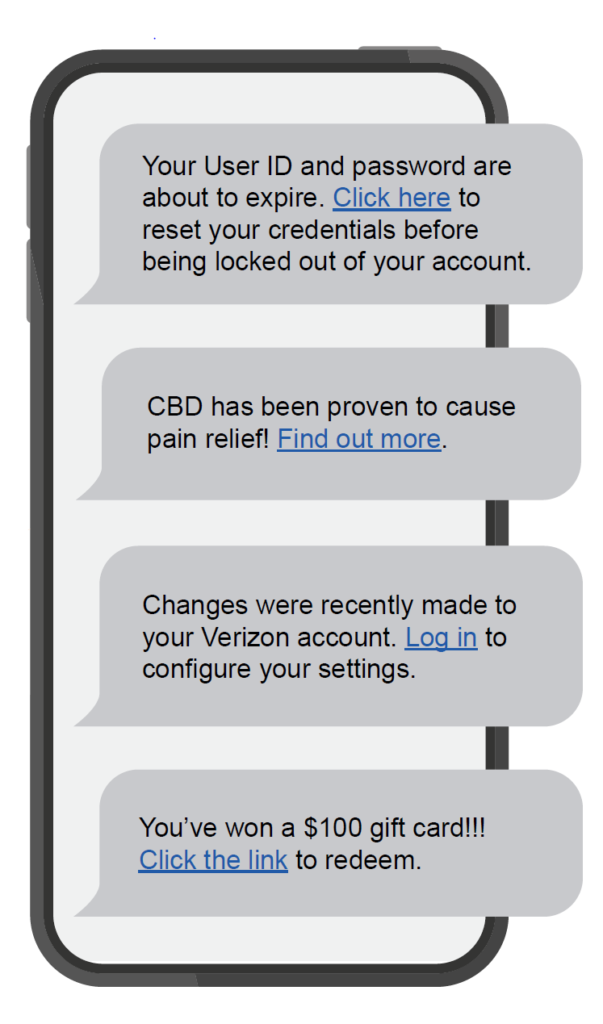
DID YOU KNOW?
SMS open rates hover around 98%. Compare that to around 20% for email, and it’s clear why cyber criminals like smishing
Search engine phishing sites often promise amazing deals, career advancement opportunities, or low interest rates for loans. Remember, if it seems too good to be true, it probably is.
Vishing involves a fraudulent actor calling a victim pretending to be from a reputable organisation and trying to extract personal information, such as banking or credit card information.
Most often, the “caller” on the other line obviously sounds like a robot, but as technology advances, this tactic has become more difficult to identify.
How to avoid vishing scams
Also known as DNS poisoning, pharming is a technically sophisticated form of phishing involving the internet’s domain name system (DNS). Pharming reroutes legitimate web traffic to a spoofed page without the user’s knowledge, often to steal valuable information.
Did you know…
DNS acts as the phonebook of the internet, taking a long string of numbers—the IP address—and translating it to the URLs we all know, like amazon.com. When cybercriminals interfere with this communication, it’s known as DNS poisoning.
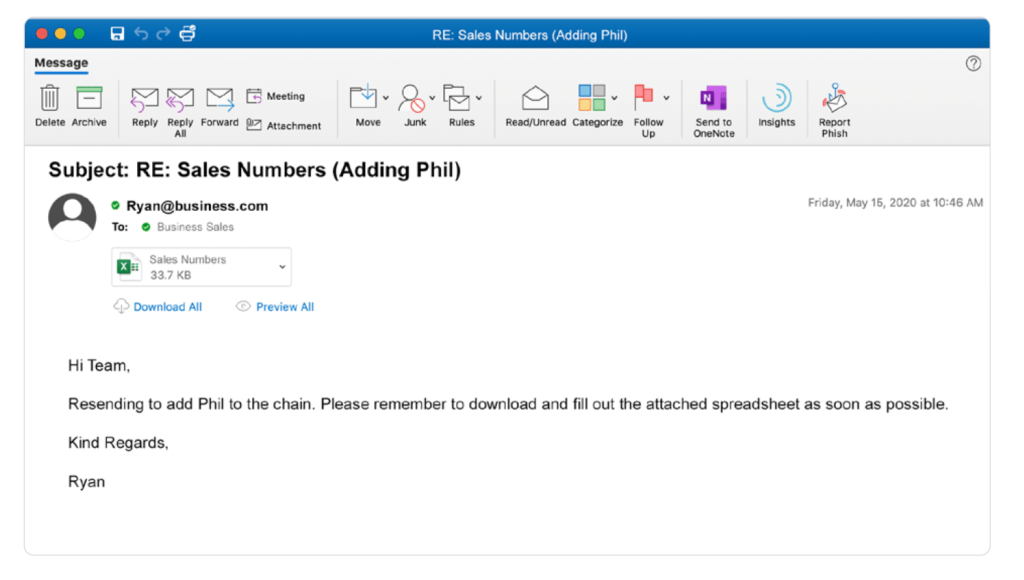
In this type of attack, a shady actor makes changes to an existing email, resulting in a nearly identical (cloned) email but with a legitimate link, attachment, or other element swapped for a malicious one. These attacks can’t get off the ground without an attacker first compromising an email account, so a good defense is using strong, unique passwords paired with two-factor authentication. Example below:
A man-in-the-middle attack involves an eavesdropper monitoring correspondence between two unsuspecting parties. When this is done to steal credentials or other sensitive information, it becomes a man-in-the-middle phishing attack.
These attacks are often carried out by creating phony public WiFi networks at coffee shops, shopping malls, and other public locations. Once joined, the man in the middle can phish for info or push malware onto devices.
One of the most expensive threats facing businesses today is business email compromise. This involves a phony email usually claiming to be an urgent request for a payment or purchase from someone within or associated with a target’s company.
Did you know…
Of the $3.5 billion the FBI estimates businesses lost to cybercrime in 2019, nearly half ($1.7 billion) was blamed on business email compromise.
Protecting yourself from phishing attacks starts with knowing what’s out there. In fact, according to Webroot research, ongoing security awareness training can help reduce breaches by nearly 70%.
Penntech IT Solutions offers Security Awareness Training to protect your business. Read the 7 steps for Effective Security Awareness Training for more information and get your FREE 14 day trial. You can can calculate the costs after the free trial below.
You need the best IT support in London. Technology is complicated and expensive. It’s so hard to maintain everything and know what to do when something breaks or goes wrong. IT problems can put a damper on your day. They’re frustrating, time-consuming, and seem like a never-ending cycle of issues.
Penntech’s average NPS score over 90 days is 84. The average Net Promoter Score (NPS) for IT Managed Service Providers (MSPs) can vary. Still, an NPS of around 50 is considered excellent in this industry, with scores above 70 exceptional and rare.
We offer our services on a trial basis for the first three months because we’re confident in our delivery and approach.
Penntech offers a wide range of IT services, from strategic project management to 24/7 remote support, ensuring all your IT needs are always covered.
We provide advanced cybersecurity measures and expertise, including penetration testing services and Cyber Essentials, to protect clients from cyber threats.
We offer Clients the ability to scale IT services up or down based on their needs. This flexibility is crucial for businesses that experience seasonal changes or rapid growth.
Other providers often enforce their preferred IT stack, but we don’t, as IT is not a one-size-fits-all solution.
We ensure our Clients’ business continuity through robust disaster recovery and backup solutions.
With experience in various verticals and industries, Penntech understands different businesses’ unique IT challenges and can provide customised solutions..
Contact us today or explore the range of support packages on offer.


Business owners often have to wear many hats, from handling HR and marketing tasks to managing the finances. One task…

Cool Windows 11 Features That May Make You Love This OS
Microsoft released the Windows 11 operating system (OS) over a year ago. It was well-received mainly with reviews as stable…

6 Ways to Prevent Misconfiguration (the Main Cause of Cloud Breaches)
Misconfiguration of cloud solutions is often overlooked when companies plan cybersecurity strategies. Cloud apps are typically quick and easy to…

4 Proven Ways to Mitigate the Costs of a Data Breach
No business wants to suffer a data breach, but unfortunately, it’s difficult to avoid them in today’s environment. Approximately 83%…

The benefits of AI include advancing our technology, improving business operations, and much more. Adoption of AI has more than doubled…

Leading Password Managers for Personal and Business
We hope that your business is already considering a password manager system, but there’s still the matter of finding the…

What’s Changing in the Cybersecurity Insurance Market?
Cybersecurity insurance is still a pretty new concept for many SMBs. It was initially introduced in the 1990s to provide coverage for large enterprises. It covered things like data processing errors and online media.

What are the advantages of implementing Conditional Access?
It seems that nearly as long as passwords have been around, they’ve been a major source of security concern. Eighty-one…

Cybersecurity Review 2023: Top Threats and Trends
As we delve into 2023, the cybersecurity landscape has never been more dynamic and crucial to our digital lives. From…

Essential Cybersecurity Tips to Safeguard Your Digital
In today’s hyper-connected world, protecting your digital life is more crucial than ever. With cyber threats lurking around every corner,…

Cybersecurity Guidelines: Must-Know Tips!
In an increasingly digital world, protecting your online presence is more critical than ever. Cybersecurity breaches are no longer just…

Cybersecurity Steps to Secure Your Data
In today’s digital age, protecting your data is more critical than ever. Cyber threats are constantly evolving, and it’s crucial…

Cybersecurity: Navigating Emerging Threats and Opportunities
In today’s digital age, cybersecurity has become a critical concern for businesses and individuals alike. As technology continues to evolve,…

How Service Cloud Transforms Customer Experience
In today’s competitive business landscape, delivering exceptional customer experiences is paramount. Service Cloud, a powerful customer service platform, has revolutionised…

A Comprehensive Guide to Cybersecurity Audits for Businesses
In today’s digital age, cybersecurity is of utmost importance for businesses. Cybersecurity audits play a crucial role in protecting sensitive…

IT Service Management for Modern Businesses
In today’s digital age, IT Service Management (ITSM) has become a cornerstone for modern businesses. As companies increasingly rely on…

Essential Skills Every Cybersecurity Engineer Must Master
In the ever-evolving field of cybersecurity, engineers must arm themselves with a diverse array of skills to defend against the…