IT Services & Cyber Security


This includes computers, networks, and data. As a result, IT Security can be tightened up in many of ways and we can find the solution that solves your problem. Whether it’s ransomware, spyware or viruses we’ve got you covered.
Do you need or want to be Cyber Essentials Certified? You can reach out to us. We’re accredited to carry out Cyber Essentials audits. We get you ready to gain certification.
Penetration testing will protect you business. Alongside robust security software, regular network penetration tests play a critical role, and these tests are precisely what cybersecurity insurers will look for when assessing your policy.
Contact Penntech today for more information and advice on IT Services & Cybersecurity services.

Cyber Essentials is a scheme backed by the British Government which helps you guard against the most common security threats and demonstrate your commitment to Security.
Security attacks come in many shapes and sizes, but the vast majority are very basic in nature and are carried out by relatively unskilled individuals. They’re the equivalent of a thief trying your front door to see if it’s unlocked.
Why should you be Cyber Essentials certified?
There are many reasons to be secure, not least to protect your own business collateral. If you tender for Government contracts, certification is likely a mandatory condition. If your client base shares sensitive information with you, certification will give you a competitive edge through the confidence it delivers.
Our role at Penntech IT Solutions is to audit and implement compliant security on your infrastructure, enabling your business to become accredited.
Our Clients tells us we’re deliver expectional service but check out the reasons below.
Flexible Packages
Flexible packages to suit your budget
We offer flexible options tailored to your business needs, whether you need ad hoc support, a block of hours, or fully managed services.
Cost Efficiency
Managing Costs in your business is critical to profitability
Clients benefit from having a dedicated IT team that acts as an extension of their business, providing personalised and consistent support. Outsourcing IT provides cost savings compared to maintaining an in-house IT Department.
Cross Industry Expertise
We have experience cross-industry
With experience in various verticals and industries, Penntech understands different businesses’ unique IT challenges and can provide customised solutions.
Disaster Recovery
Continuity planning is critical to your business
We ensure our Clients’ business continuity through robust disaster recovery and backup solutions.
Tech not Sales Focus
Cost-effective solutions that are right for your business
Other providers often enforce their preferred IT stack, but we don’t, as IT is not a one-size-fits-all solution.
Client Satisfaction Rates
Our average score is 84 with an industry average of 50 considered to be excellent
Penntech’s average NPS score over 90 days is 84. The average Net Promoter Score (NPS) for IT Managed Service Providers (MSPs) can vary. Still, an NPS of around 50 is considered excellent in this industry, with scores above 70 exceptional and rare.
Trial Periods
No lengthy ties-ins and a trial period
We offer our services on a trial basis for the first three months because we’re confident in our delivery and approach.
24/7 Support
Knowing you’re covered anytime brings peace of mind
Penntech offers a wide range of IT services, from strategic project management to 24/7 remote support, ensuring all your IT needs are always covered.
Cybersecurity Expertise
Security to keep your business safe
We provide advanced cybersecurity measures and expertise, including penetration testing services and Cyber Essentials, to protect clients from cyber threats.
Scalability
We ensure you can scale up or down based on business needs
We offer Clients the ability to scale IT services up or down based on their needs. This flexibility is crucial for businesses that experience seasonal changes or rapid growth.
Let’s do something good together. If you share your problem, we’ll give you our solution all hassle-free! A problem shared is a problem halved.

Email protection and security is essential to avoid phishing attacks which are on the rise. Did you know that over 91% of cyber attacks start with email?

Our suite of encryption tools can be centrally managed and applied to laptops, desktops, mobile devices and USB sticks.

Our suite of encryption tools can be centrally managed and applied to laptops, desktops, mobile devices and USB sticks.

AntiVirus for business and Cybersecurity are critical and not just a nice to have. Discover cloud-based protection that stops threats in real-time and secures businesses and individuals wherever they connect.

Is your business data secure when it leaves the office? Do you have Mobile Device Encryption in place?

Multi-factor authentication can also be called two-step verification or 2-factor authentication (2FA).

Multi-factor authentication can also be called two-step verification or 2-factor authentication (2FA).
We provide support and solutions to the most challenging IT problems. Read what our clients have to say about us and how we helped them.

Office 365 is the world’s most popular app. It’s fast, powerful, integrated with other Microsoft apps, and available across devices. We’re proud to be a Microsoft Silver Partner.
How accreditation is achieved?
We had to meet Microsoft’s rigorous standards and demonstrate the highest standard of technical performance, service quality and customer care across four key areas:
And we had to prove our technical knowledge through certified qualification across our team.

Increase your cybersecurity posture and adhere to the most crucial best practices and standards with Cyber Essentials certified solutions.
Cyber Essentials is a scheme backed by the British Government which helps you to guard against the most common security threats and demonstrate your commitment to Security.
Security attacks come in many shapes and sizes, but the vast majority are very basic in nature and are carried out by relatively unskilled individuals. They’re the equivalent of a thief trying your front door to see if it’s unlocked.
We’re proud to be a Premier Plus member of the London Chamber of Commerce
Nam dapibus nisl vitae elit fringilla rutrum. Aenean sollicitudin, erat a elementum rutrum, neque sem pretium metus, quis mollis nisl nunc et massa. Vestibulum sed metus in lorem tristique ullamcorper id vitae erat.

Penntech modernised the SharePoint Intranet to align to business strategy and objectives.

Penntech configured Microsoft Endpoint Configuration Managed MECM to ensure accurate reporting and simplification of day-to-day IT tasks.

Penntech transitioned to a cloud-first infrastructure model, significantly improving scalability, performance and costs.
MECM Segregation of multiple networks with VLAN
Penntech established two MECM servers to ensure localised management, redundancy, and improved load distribution.
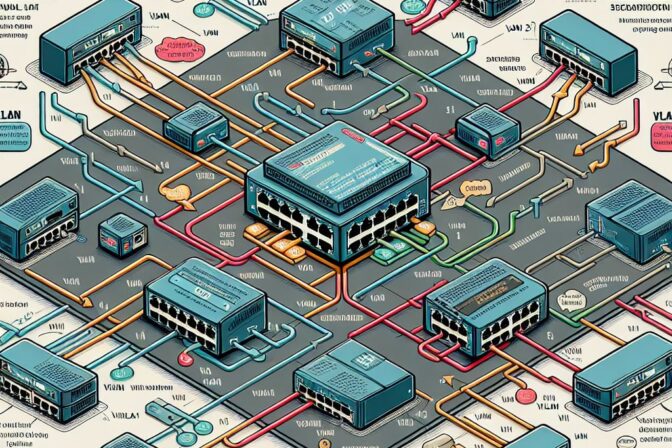
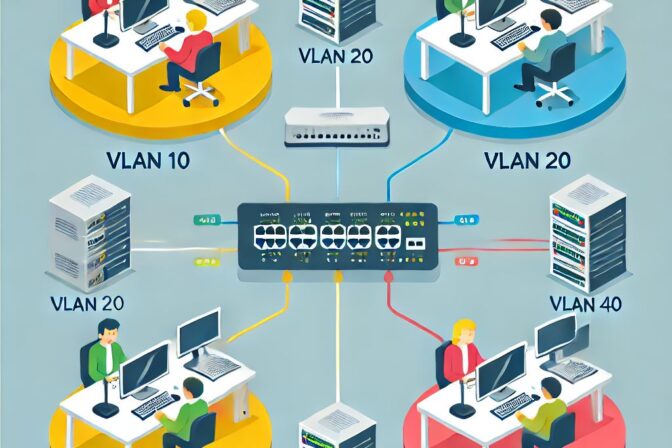
Segregation of multiple networks with VLAN
Penntech completed a full network audit of the current setup to build a full picture of the infrastructure.
A virtualised network was created on the existing hardware across the access, distribution and core switches.

Massive was asked by a client to provide a Cyber Insurance policy. Rather than simply getting a policy they used this request to become compliant with Cyber Essentials.

Protect your business with our top-tier Cybersecurity Solutions. Contact us today to safeguard your data and ensure your operations remain secure.
Or give us a call
+44 (0) 2033 711 810